Troubleshooting with Apstra
Configuration Deviation Detection
Understanding Configuration Anomalies
One of Apstra’s most powerful capabilities is its ability to detect when a network device’s configuration has deviated from the intended state. This is crucial for maintaining the integrity of your network and ensuring that unauthorized or accidental changes don’t go unnoticed.
In this exercise, we’ll simulate a configuration change outside of Apstra’s control and observe how the system detects and alerts you to this deviation.
Scenario: Detecting Unauthorized Configuration Changes
Imagine that a network engineer has made a direct change to one of your switches without going through Apstra. This could be an emergency fix, an unauthorized change, or simply a mistake. Let’s see how Apstra handles this situation.
Task: Observe Configuration Deviation Detection
Step 1: Simulate a Configuration Change
-
Go to your CloudLabs portal, and toggle the Insert a Configuration Change slider
The slider will turn green and you will see a confirmation message:
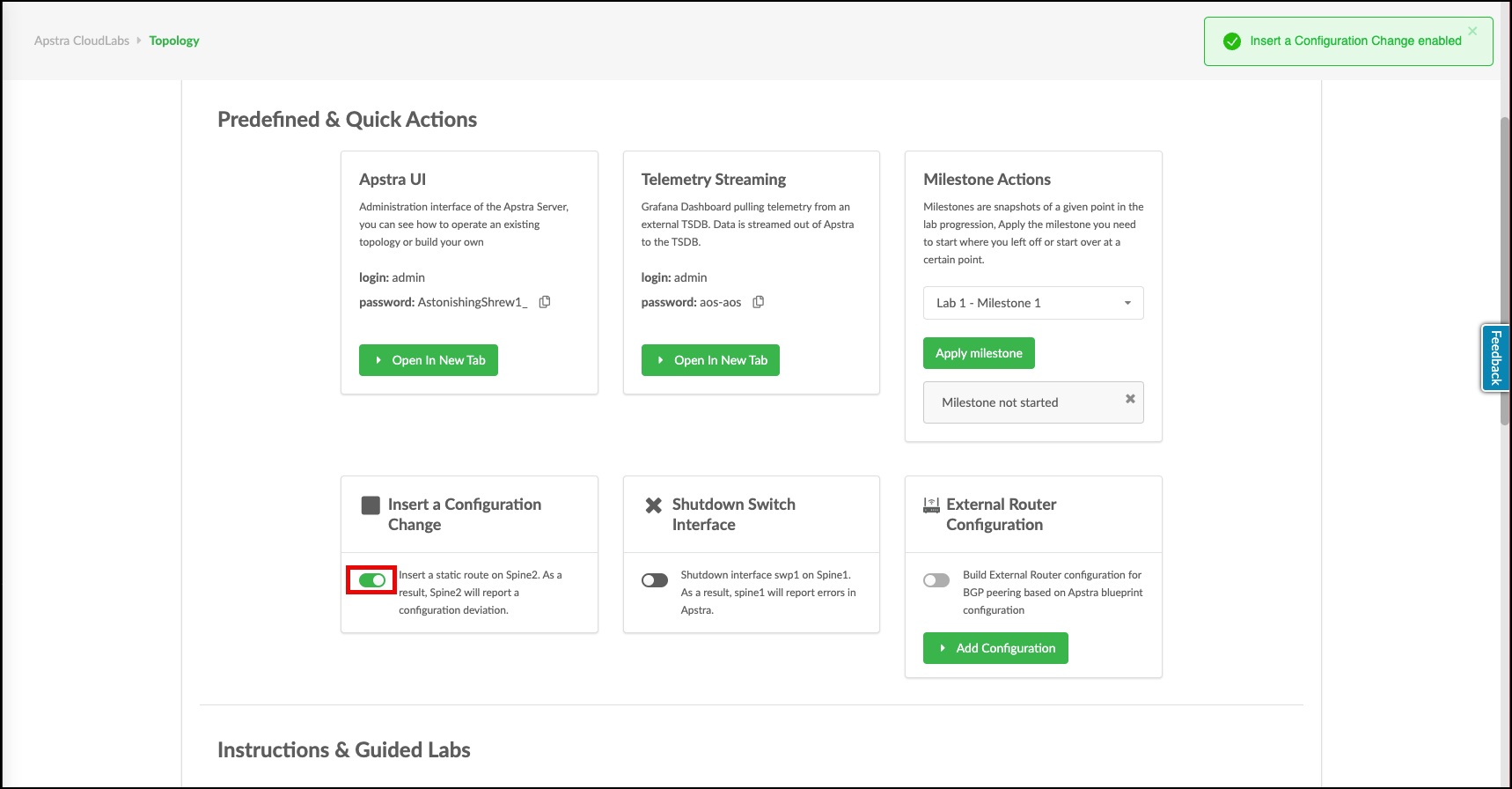
Behind the scenes, this simulates a configuration change being made directly on one of your spine switches.
Step 2: Observe the Anomaly Detection
-
Return to the Apstra UI and wait a moment
Apstra continuously validates the actual configuration of managed devices against its intended state model.
-
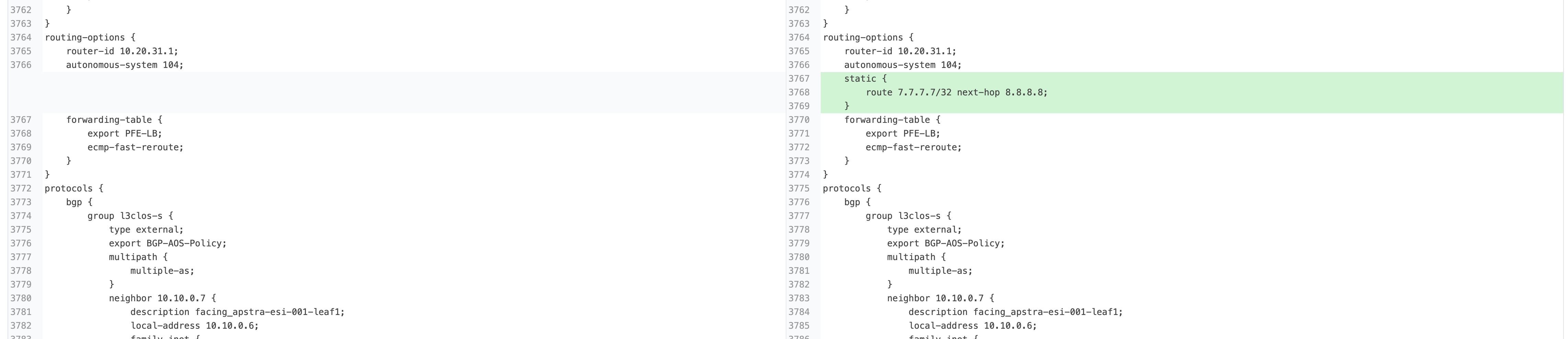
Soon, a configuration deviation anomaly will appear. Notice the red indicators that highlight where issues have been detected
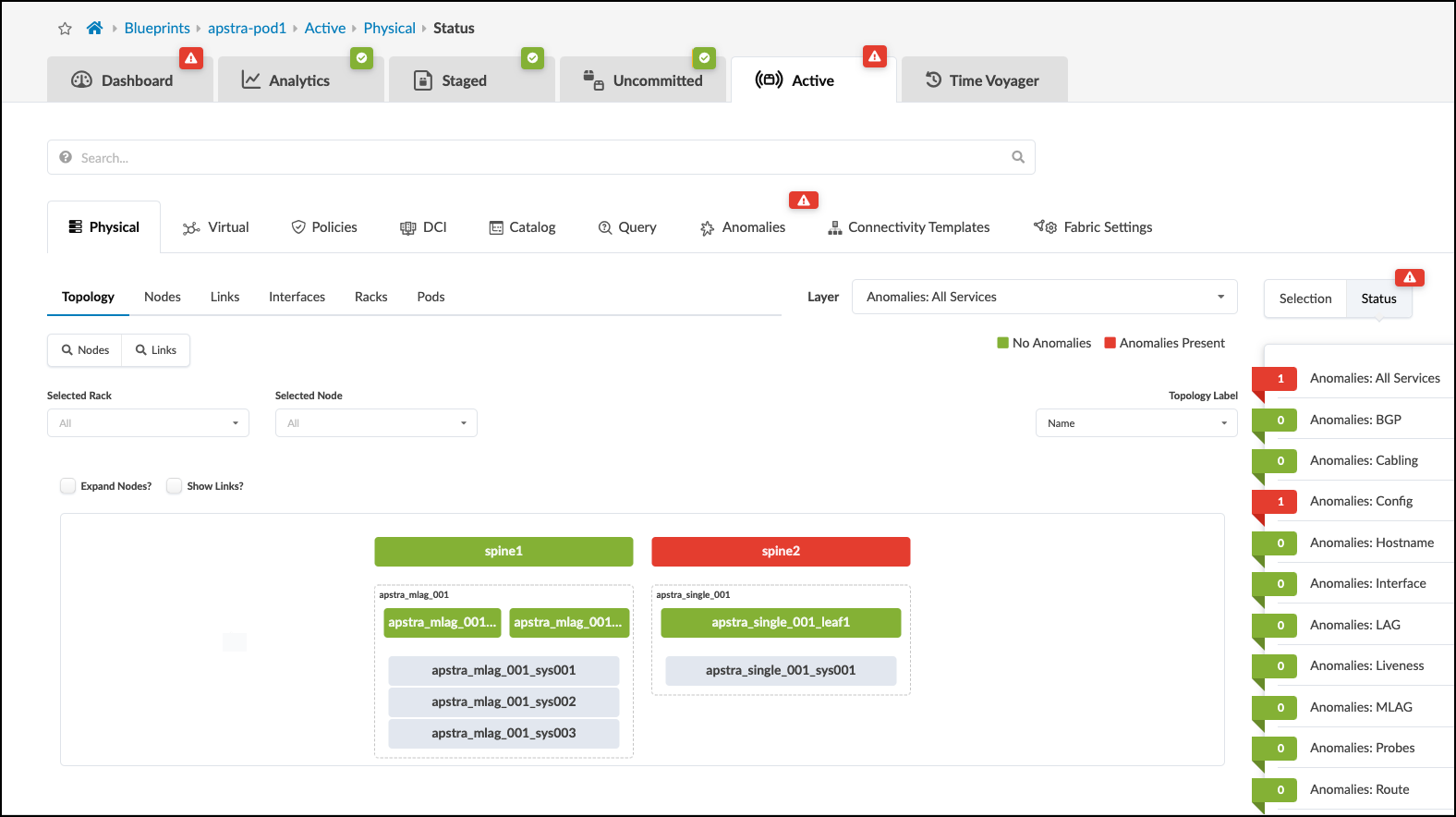
These indicators show Apstra’s ability to detect discrepancies between its intent model and the actual network state.
Step 3: Investigate the Anomaly
-
Click the Anomalies tab to move to the Anomaly Details view
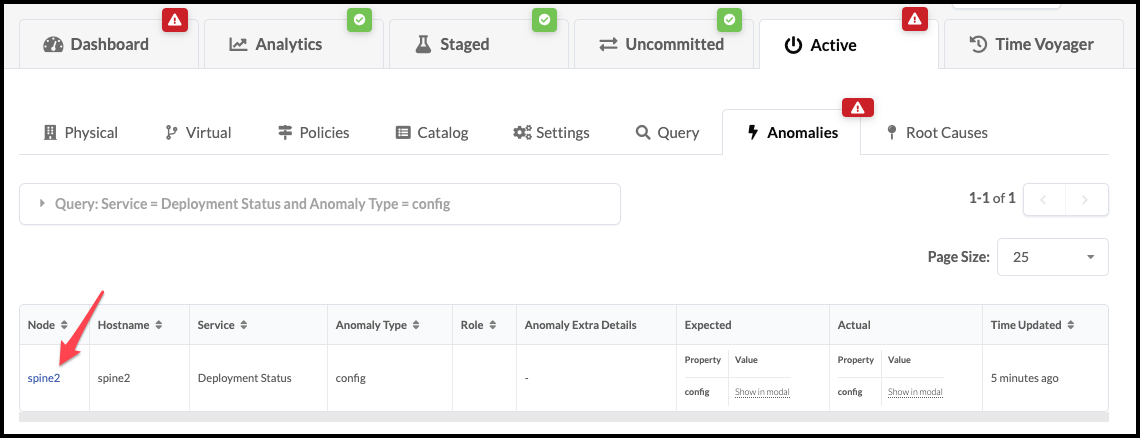
This view provides a centralized list of all detected anomalies across your fabric.
-
Click spine2 to go to the telemetry view for the affected device
This view shows all anomalies detected for this specific device.
-
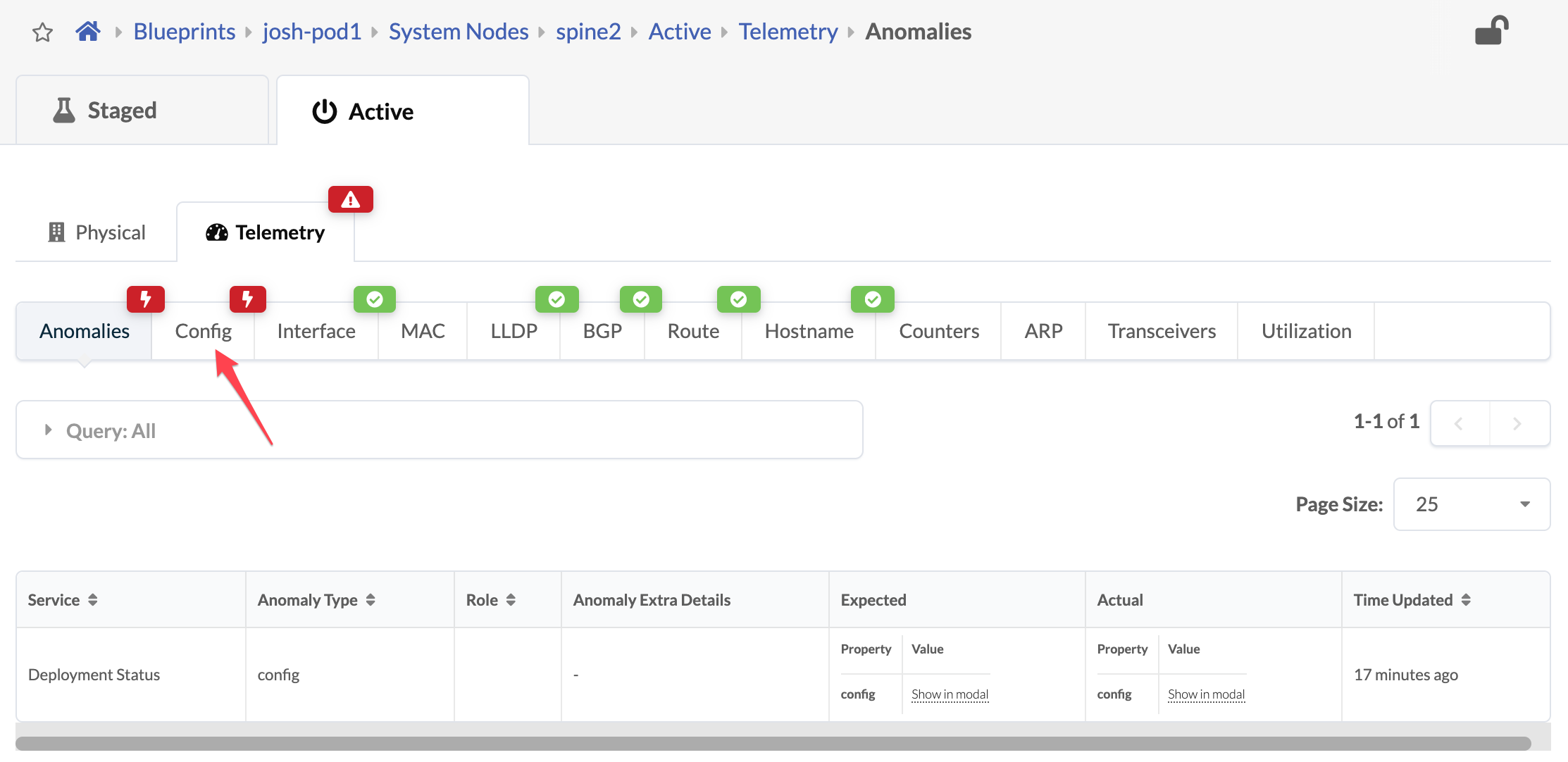
Click the Config tab to see the anomaly’s details. Scroll down to see the configuration deviation
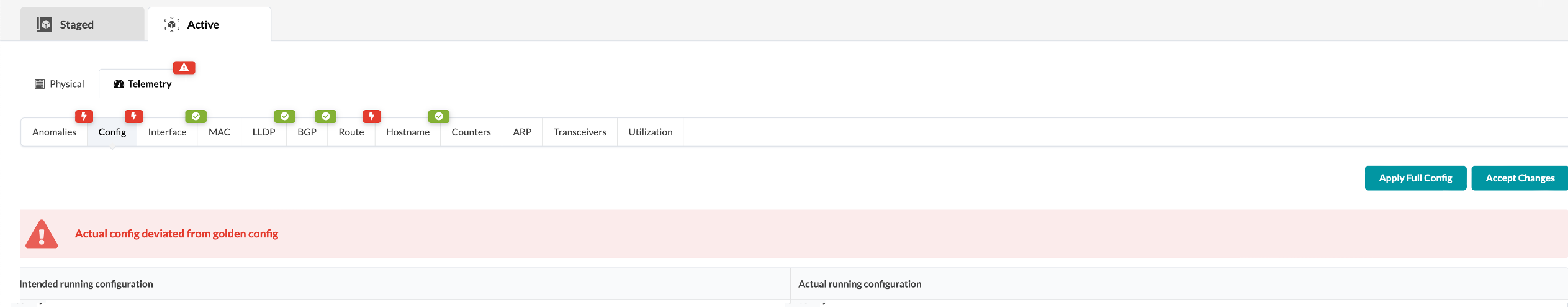
Apstra shows you exactly what has changed, comparing the expected configuration with the actual configuration on the device.
Step 4: Resolve the Configuration Deviation
In a real environment, you would have two options when you discover a configuration deviation:
-
Accept the Change: If the change was intentional and should be incorporated into your intent model, you can click the Accept Changes button to update Apstra’s model.
-
Revert the Change: If the change was unauthorized or incorrect, you can click the Apply Full Config button to push the correct configuration back to the device.
For this exercise:
-
Return to the CloudLabs portal and toggle off the Insert a Configuration Change slider
This simulates correcting the unauthorized change.
-
Return to the Apstra UI and observe that the anomaly is cleared automatically
Why This Matters
This capability demonstrates several key benefits of Apstra’s intent-based approach:
-
Continuous Validation: Apstra constantly compares actual device configurations with the intended state
-
Immediate Detection: Changes made outside of Apstra are quickly identified
-
Precise Reporting: The exact configuration discrepancy is highlighted
-
Remediation Options: You can either incorporate or revert changes as appropriate
In a traditional network, unauthorized configuration changes might go undetected until they cause problems. With Apstra, these deviations are immediately flagged, allowing you to maintain the integrity of your network design and prevent potential issues before they impact services.
Direct CLI Access for Troubleshooting
While Apstra provides comprehensive visibility through its UI, sometimes you need to execute specific CLI commands on a device for deeper troubleshooting or verification. Apstra makes this simple by providing direct CLI access to managed devices right from the interface.
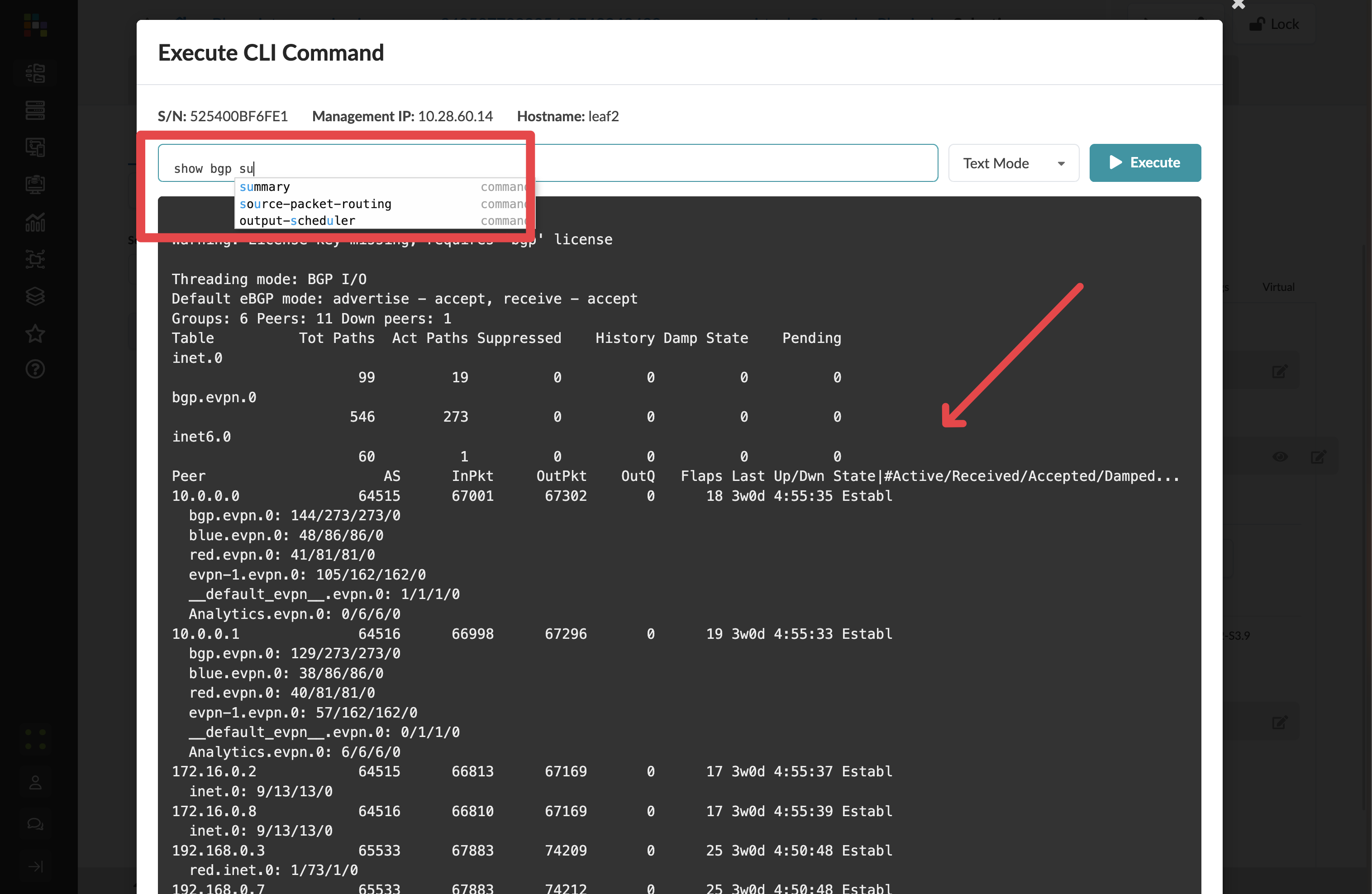
Accessing the CLI Command Interface
-
Navigate to Staged > Physical > Topology
-
Click on the device you want to troubleshoot (in this case, select a leaf switch)
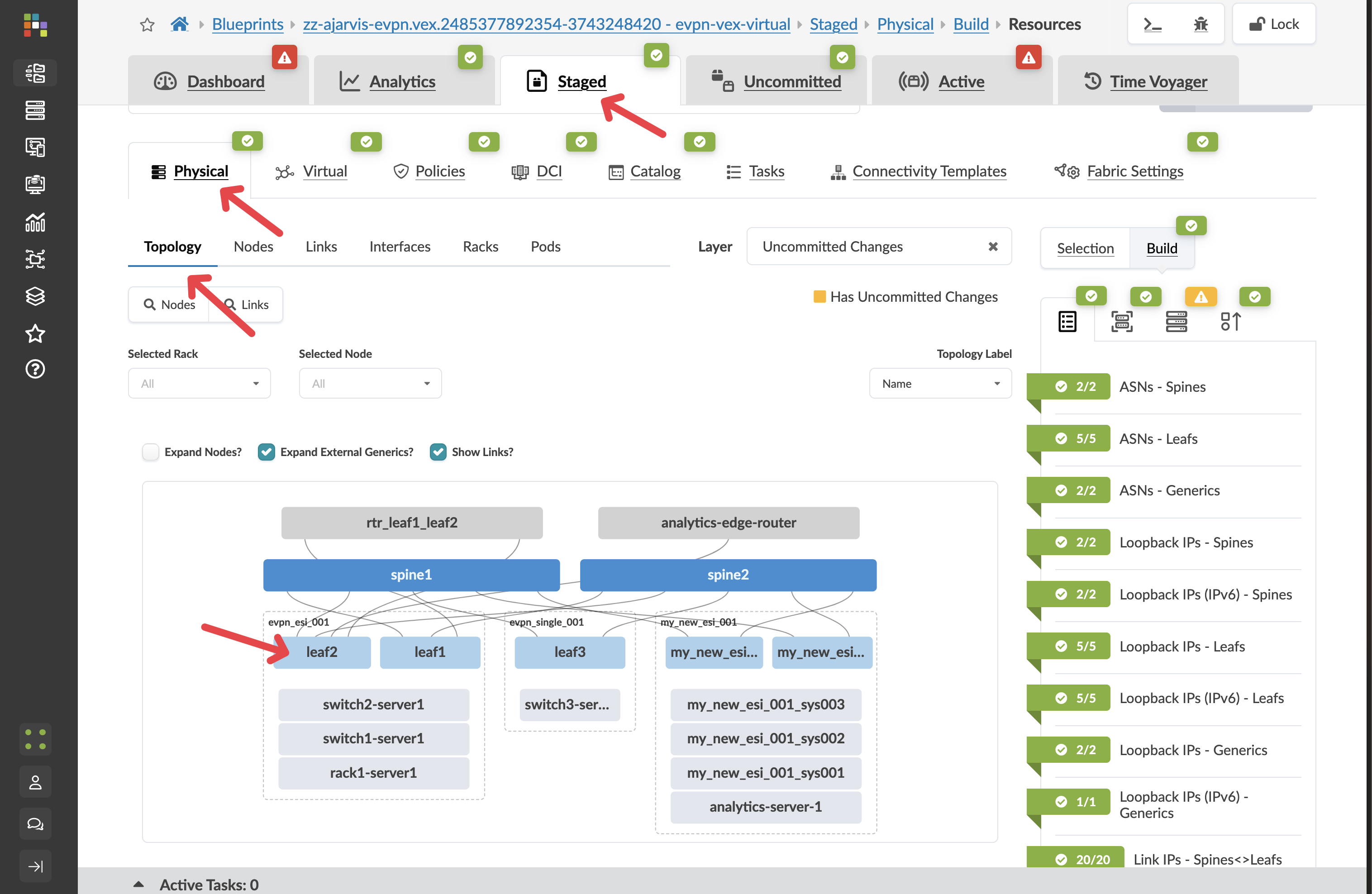
-
In the device details panel on the right side, locate the Device Info section
-
Find and click the _Execute CLI Command option
This option gives you direct CLI access to the selected device without having to establish a separate connection.
Using the Context-Aware CLI
The CLI interface in Apstra has several powerful features that make troubleshooting more efficient:
-
The CLI is context-aware for Junos devices, providing auto-completion of commands
This means you can start typing a command and press Tab to see available options, just like on the native Junos CLI.
-
You can execute any show commands to verify device state, for example:
show interfaces brief show bgp summary show route table show evpn instance -
Output is displayed directly in the Apstra UI, allowing you to quickly analyze results
Benefits of Integrated CLI Access
This integrated CLI access provides several advantages:
-
Efficiency: No need to establish separate SSH sessions to devices
-
Context: You’re already looking at the device in Apstra, so you have full context of its role and configuration
-
Authentication: No need to manage separate credentials for CLI access
-
History: Command history is maintained during your session
When to Use Direct CLI Access
While Apstra’s UI provides most of the information you need, direct CLI access is valuable for:
-
Verifying specific protocol states in detail
-
Checking counters or statistics not surfaced in the UI
-
Validating that configuration changes have taken effect
-
Troubleshooting transient issues
-
Gathering additional diagnostic information
This capability bridges the gap between Apstra’s intent-based management and traditional CLI-based troubleshooting, giving you the best of both worlds when diagnosing network issues.
What You’ve Learned
In this troubleshooting section, you’ve seen how Apstra:
-
Continuously validates actual device configurations against intended state
-
Immediately detects and alerts on configuration deviations
-
Provides detailed information about what changed
-
Offers options to either accept or revert changes
-
Gives direct CLI access to devices for deeper troubleshooting
-
Provides context-aware CLI with auto-completion for efficient command execution
These powerful troubleshooting capabilities ensure that you can quickly identify and resolve issues in your network, whether they’re related to configuration deviations or require deeper investigation at the CLI level.